Understanding the TLS Handshake: What Happens Behind the Lock Icon 🔒
When you browse the web, the little padlock symbol represents security and trust. But have you ever wondered what processes occur behind the scenes to establish this secure connection? In this blog post, we will dissect the TLS (Transport Layer Security) Handshake, which forms the backbone of secure online communication.
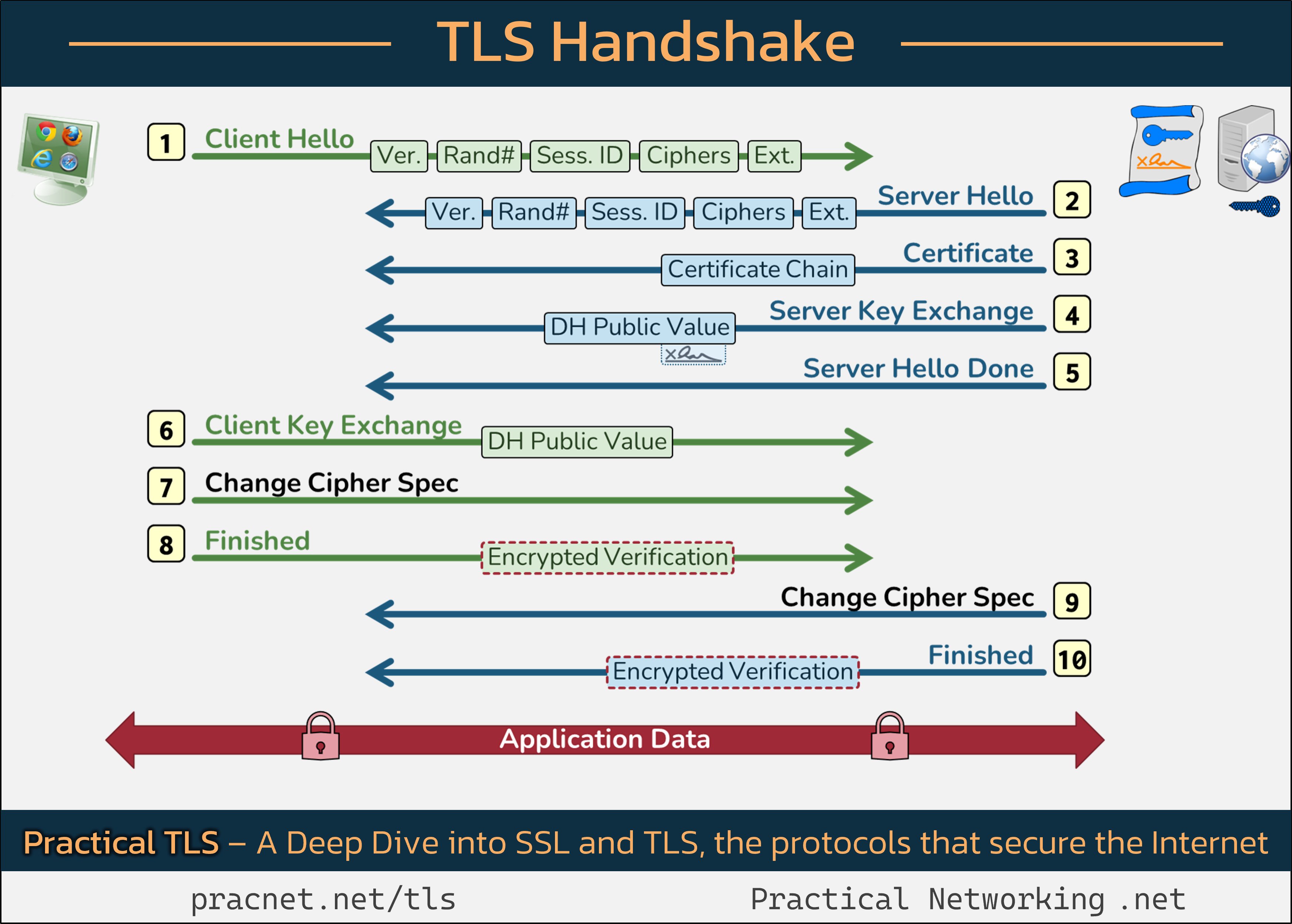
The infographic linked below provides a visual representation of the messages exchanged between your web browser (the Client) and the website’s server during a TLS session:
It’s beneficial to have this image open in a separate tab as we delve into the handshake process.
The Purpose of SSL/TLS
Before we get started, it’s important to highlight the primary goals of SSL/TLS:
- ✅ Verify the authenticity of the Server
- ✅ Establish session keys that ensure secure data transfer
Now, let’s go through the different records that comprise the TLS Handshake.
1️⃣ Client Hello
The TLS Handshake begins when the Client initiates a Client Hello message. This message contains five critical fields:
- SSL Version
- Random Number
- Session ID
- Cipher Suites
- Extensions
Each field plays an essential role in achieving a secure connection.
1️⃣.1 – SSL Version
The Client specifies the highest SSL/TLS version it supports, such as SSL 3.0, TLS 1.0, TLS 1.1, or TLS 1.2. The Server replies with its supported version, and they select the highest common one to establish a secure connection. As of now, only TLS 1.2 and TLS 1.3 are considered secure.
1️⃣.2 – Random Number
The Client generates a 32-byte random value that is mixed into the session keys, adding an element of entropy to enhance security.
1️⃣.3 – Session ID
This is used for “Session Resumption,” allowing clients and servers to bypass heavy cryptographic operations if they are resuming a previous session. However, for this explanation, we’ll assume a full handshake takes place.
1️⃣.4 – Cipher Suites
A Cipher Suite includes algorithms used for Authentication
Share this content:



Thank you for sharing this detailed overview of the TLS handshake process. Understanding TLS is essential for diagnosing secure connections issues and ensuring your website’s security protocols are correctly configured.
If you’re experiencing problems with the TLS handshake, here are some troubleshooting steps you can follow:
1. **Verify Server Configuration:** Ensure your web server is configured to support TLS 1.2 and TLS 1.3, as older versions like SSL 3.0 and TLS 1.0 are deprecated and insecure.
2. **Check SSL/TLS Certificates:** Make sure your SSL certificates are valid, not expired, and properly installed. You can use tools like SSL Labs’ SSL Server Test to get an in-depth analysis.
3. **Update Your Server & Browser:** Keep your server software and web browsers up to date to support the latest security protocols and cipher suites.
4. **Review Cipher Suites:** Confirm that your server is configured to support secure cipher suites, avoiding weak or deprecated ones.
5. **Analyze Network Logs:** Check server logs for TLS handshake errors which might indicate certificate issues, protocol mismatches, or cipher suite incompatibilities.
If you’re using WordPress and facing SSL issues, also ensure that your plugins are up to date and that your `force SSL` settings are correctly configured in your site and hosting environment.
Let me know if you need guidance on configuring your server’s TLS settings or further troubleshooting steps. I’m here to help ensure your website maintains a secure and trustworthy connection for your visitors.