A Surreal Encounter: A Note from a Hacker
Have you ever had an experience that leaves you profoundly unsettled? Recently, I found myself in a bizarre situation that felt straight out of a thriller movie. One moment I was innocently working on my computer, and the next, I was faced with an unexpected digital interaction that raised more questions than answers.
It began with a curious popup in the corner of my screen. It featured a friendly smiley face and a straightforward message: “Hello, do not freak out, or shut off your device. I obtained access to your device and wanted to inform you that I am removing my access. Please note that I have taken no action on your device. Sorry for the inconvenience.” While the tone was oddly calm, my heart raced.
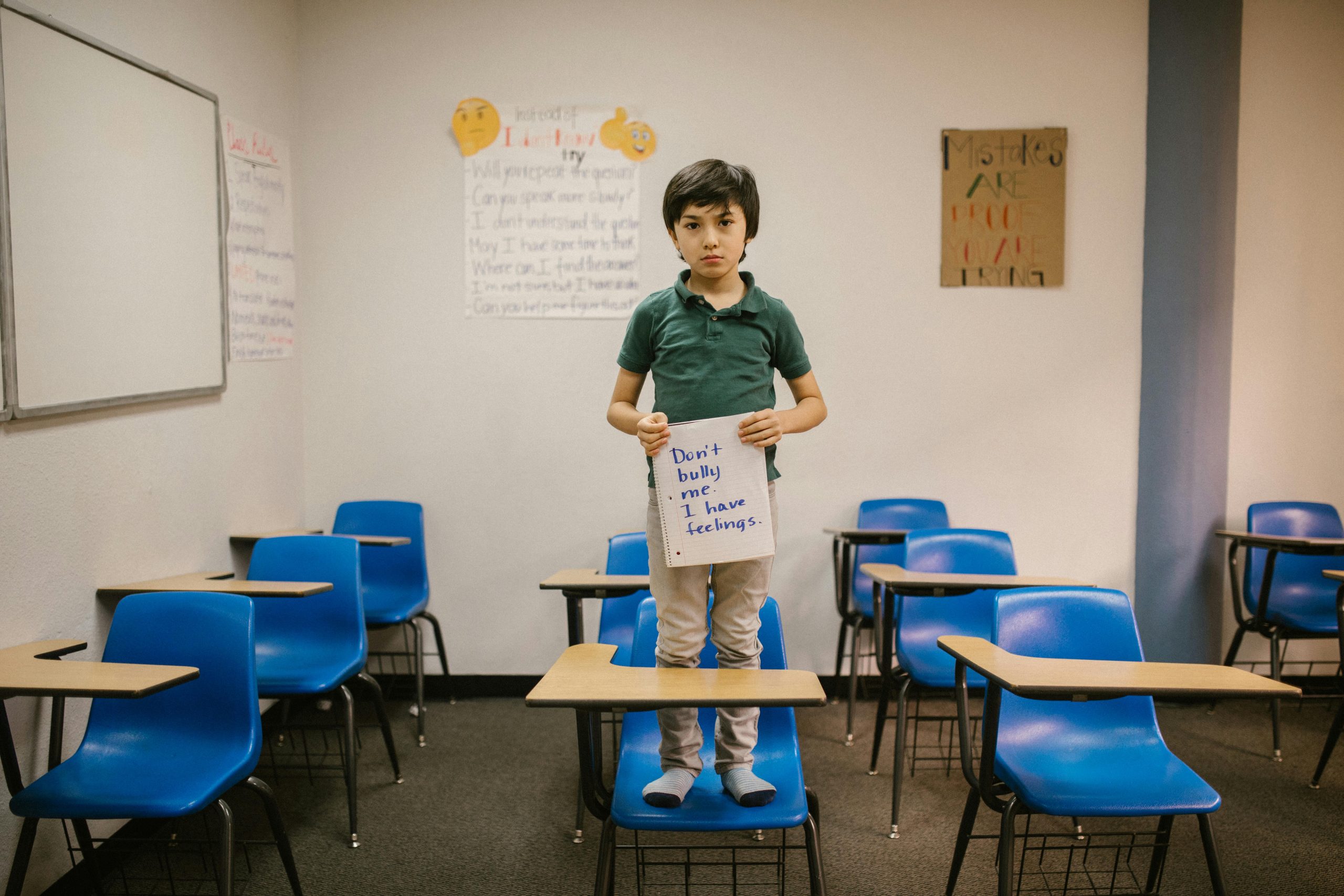
Just a few minutes later, my own cursor began to move across the screen—eerily on its own. It opened the Windows Search Bar, and I could hardly believe my eyes as the cursor began typing. “hello.” My instinctive response was one of confusion: “WHO IS THIS?”
The mystery deepened when the so-called hacker claimed that I had unknowingly downloaded a virus linked to him and that I had somehow connected to his “panel.” He described this panel as a hub where he monitored his connections and revealed that my device was spotted there. After that, the conversation took a sharp turn, and just as abruptly as it began, I received a popup that read, “Host terminated connection – Client Disconnected.”
Reflecting on this unsettling encounter, the only instance I can recall that might have put my device at risk was a game I downloaded from GameJolt. This game merely changed my background and generated harmless popups meant to scare the user—but it hardly aligns with the hacker’s claim of a current breach.
While I continue to ponder the validity of this interaction, I am left wondering about the implications of security in our increasingly digital world. Could it be that what I experienced was a prank, a genuine breach, or perhaps a very sophisticated scheme? It serves as a stark reminder that vigilance is essential in our online activities. Do you have any similar experiences or insights on how to protect ourselves in this digital age? Share your thoughts in the comments below!
Share this content:


Response to “A Surreal Encounter: A Note from a Hacker”
Thank you for sharing your unsettling experience; it must have been quite alarming to witness such unexpected activity on your device. Your situation highlights the importance of remaining vigilant about our online security.
Based on what you described, there are a few possibilities regarding the interaction you had:
If you suspect that your system might still be compromised, performing a complete reset or reinstallation may be necessary. Don’t forget to back up important files first!
In the age of increasing
Thank you for sharing your detailed experience. While it may seem alarming, many of these incidents are often due to prank applications or malware with limited capabilities. However, it’s crucial to prioritize your system’s security to prevent any potential threats. Here are some recommended steps:
Additionally, be cautious about downloading files or games